Use This Template
Use This Template
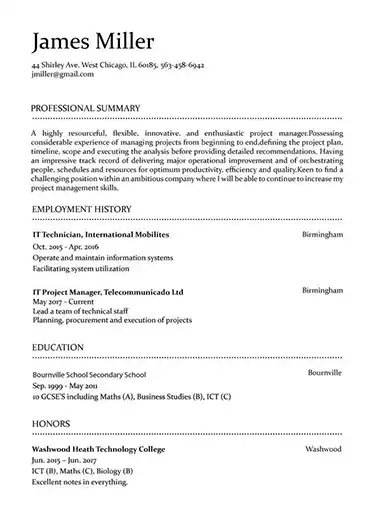
Build your resume in 15 minutes
Create an awesome resume that meets the expectations of potential employers with our selection of professional, field-tested resume templates.
security analyst: Resume Samples & Writing Guide
davis.mike@protonmail.com
832-665-3599
Employment history
- Analyze security risks and develop risk mitigation strategies
- Analyze security requirements and recommend appropriate solutions
- Perform vulnerability and risk assessments
- Develop security reports and documentation
- Stay up to date on security trends and best practices
- Coordinate and collaborate with other IT teams
- Develop and maintain security awareness training
- Analyze security risks and develop risk mitigation strategies
- Evaluate and recommend security solutions
Education
Skills
Do you already have a resume? Use our PDF converter and edit your resume.
nelsongary85@protonmail.com
884-636-9715
Professional Summary
Employment history
- Develop and implement security policies, standards, and procedures
- Evaluate and recommend security solutions
- Identify and respond to security incidents
- Prepare and present security briefings and training sessions
- Develop security reports and documentation
- Monitor security systems and networks for potential threats
- Design and implement security architectures
- Prepare and present security briefings and training sessions
- Monitor security systems and networks for potential threats
Education
Skills
jacksonquentin@mail.com
875-332-1299
Employment history
- Design and implement security architectures
- Develop and maintain security awareness training
- Develop security reports and documentation
- Analyze security risks and develop risk mitigation strategies
- Evaluate and recommend security solutions
- Monitor and report on security compliance
- Monitor and report on security compliance
- Analyze security requirements and recommend appropriate solutions
- Perform vulnerability and risk assessments
Education
Skills
jacksonroger@gmail.com
671-508-5461
Employment history
- Develop security reports and documentation
- Monitor and report on security compliance
- Design and implement security architectures
- Monitor security systems and networks for potential threats
- Perform vulnerability and risk assessments
- Coordinate and collaborate with other IT teams
- Design and implement security architectures
- Monitor and report on security compliance
- Analyze security requirements and recommend appropriate solutions
Education
Skills
rogersmith@protonmail.com
825-916-7736
Employment history
- Prepare and present security briefings and training sessions
- Develop and maintain security awareness training
- Stay up to date on security trends and best practices
- Develop and maintain security awareness training
- Develop and implement security policies, standards, and procedures
- Stay up to date on security trends and best practices
- Design and implement security architectures
- Develop security reports and documentation
- Stay up to date on security trends and best practices
Education
Skills
Not in love with this template? Browse our full library of resume templates
With demand for security analysts rising by an incredible amount, you may be thinking that it will be easy to get hired. However, that’s a dangerous mistake to make. Just because companies and government agencies alike are investing heavily in cybersecurity doesn’t mean they’ll hire just anyone. You’ll have a tremendous amount of responsibility, so you’re not going to get hired just based on some security experience.
You need to communicate your security analyst abilities and experience so a recruiter can understand it, to ensure you’ve met the requirements to get past ATS, and to get all the subtle details right to make a strong impression. Fortunately, we break down everything you need to know in this guide.
What this guide will teach you:
- How to use resume examples to get started
- What you need to do about ATS
- How to get into a recruiter’s mind and get them to choose you
- The best formatting rules to follow
- How to list your job qualifications
- What you should (and shouldn’t) include in your education section
- How to make your achievements and skills stand out from the competition
- The most effective way to start a security analyst resume
- Why targeting your resume to a specific role makes all the difference
- How to prepare for a job interview
- Why a resume builder makes the whole process easier.
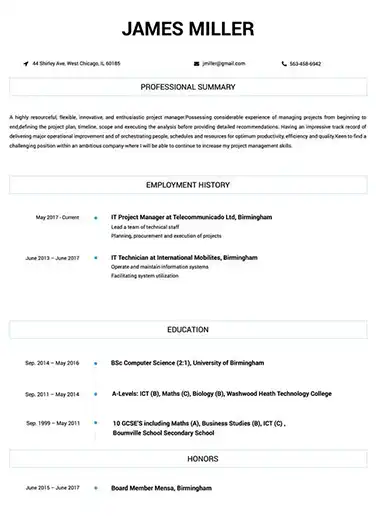
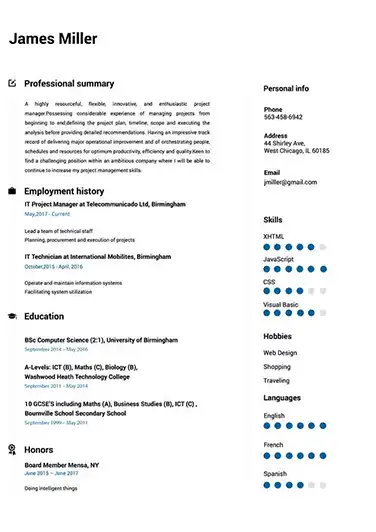
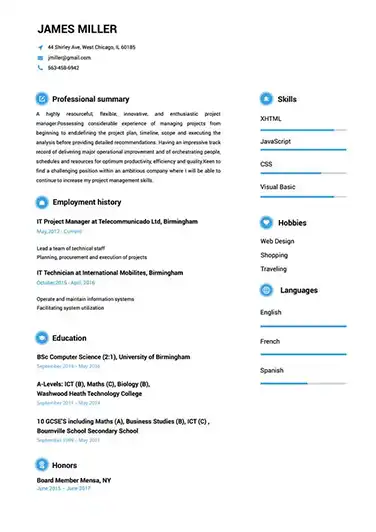
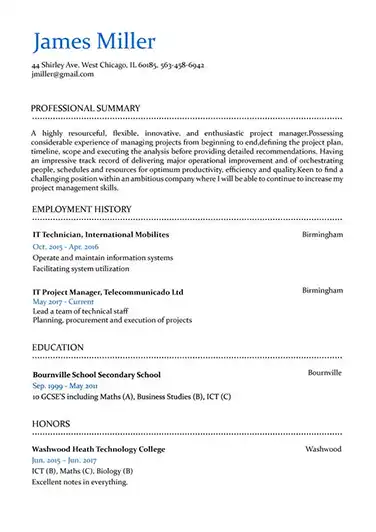
Security analyst resume template examples to get you started
With so many things to get right, you might be tempted to just get started right away. But that’s a recipe for wasted time. Before you begin writing your resume, look through some of the security analyst resume examples we’ve chosen for you.
Start taking notes about what you notice about these resumes. What’s your first impression, what stands out about them, is there anything you don’t like about them? Use these notes as a starting point for your resume. Also try imagining you’re a recruiter, you’ve looked through dozens of resumes before these ones come to your desk. How does this change how you see them? This is a mindset you’ll want to use throughout the process of creating your own resume.
[Examples]
How to write a security analyst resume that will get you the job
The reason it’s important to consider your resume from a recruiter’s perspective is that not many security analysts do. They’ll write their resumes only focusing on explaining why they’re the best candidate without considering who makes that decision and how they do it. To get chosen over them, you need to show those recruiters that you’re thinking about them.
But before you get there, you’ve got to overcome the first hurdle most resumes fail to meet these days.
Why you need to start by thinking about ATS
ATS stands for Applicant Tracking System. These systems use AI to scan huge volumes of resumes fast to save recruiters the time needed to manually review them. The problem is that these systems are far from perfect. They mistakenly reject so many resumes that around 75% of all resumes submitted today are never seen by a human.
To ensure your resume isn’t in that group, you need to understand how ATS work and plan for them. While each ATS is a bit different, they generally function by being given a set of criteria to look for in a resume. When a resume meets the minimum levels, it gets forwarded to a recruiter for review. The trick is understanding what those criteria will be and avoiding the technical reasons which can get your resume automatically rejected.
We’ve broken down how to do this into three simple steps.
- Only submit a resume in the .pdf, .doc, or .docx file formats. These are the three formats nearly all ATS are designed to read. Submitting anything else will likely lead to automatic rejection because the system won’t be able to read your resume.
- Create your resume with a specialized resume builder. ATS often have trouble with files like Word documents because the formatting confuses them. The best way to ensure your resume file can be properly read by ATS is to use a resume builder specifically designed to produce ATS-optimized files.
- Use the job description and keywords to your advantage. Obviously if you know what the ATS is looking for on your resume you’ve got an advantage. So look to the job description and list all of the experience, skills, etc. it mentions. Now, try and get as many of them on your resume as possible (without stretching the truth) and be sure to phrase them the same way they were phrased originally.
By following these steps, you’ll avoid the biggest reasons most resumes are rejected.
How to give recruiters what they’re looking for
Once you get past ATS, your resume still needs to impress a recruiter. This is where considering their perspective comes in handy. To appeal to a recruiter, you first need to know what they’re looking for and ensure it’s in your resume. Luckily, you’ve already done that for ATS.
The next thing you need to do is to make it easy for them to say “yes” to hiring or at least interviewing you as a candidate. This boils down to making sure your resume is short, well written, and has design which makes it easy to get its information across. They shouldn’t need to read through irrelevant information or re-read sentences to understand what you meant to say. Fortunately, we’ll provide examples throughout this guide showing you how to do this.
How to format a security analyst resume
The first step towards making your resume easy for recruiters is getting the formatting right. To start, you want to follow this basic rule: more important information goes towards the top. Imagine you got a security report and it mentioned a critical security flaw which could cost your employer millions around the middle of page 4. That’s far from ideal, but gives you an idea why it’s so important to consider where the most important information on your resume goes.
We’ll talk later about using a resume objective or summary to get your most important points across at the start, but this rule also means you’ll want to list your work experience in reverse chronological order: putting the most recent work at the top. All of this makes it easier for a recruiter to quickly learn what they need from your resume, something they will appreciate.
How long should it be?
You can read all kinds of advice for security analyst resumes saying how long they should be, but the best rule of thumb is: as short as possible. If you’re applying to be the head security analyst at a Fortune 500 company and you’ve got decades of experience, your resume can get away with being pretty long. The people reviewing it will be willing to take the time to read a few pages.
But for most security analyst positions, recruiters will be swamped with applications and won’t appreciate being asked to read 3+ more pages. So, try and evaluate all the information you include on your resume and ask yourself whether it’s really necessary. If not, leave it off. The result should be a shorter and more focused resume recruiters will appreciate.
Which sections should you consider including?
- Resume objective or summary
- Work experience
- Achievements
- Education and certifications
- Hard skills
- Soft Skills
What makes a great security analyst resume?
Now that we’re past all the basic rules you need to follow, what specifically makes for a standout security analyst resume? In short, it’s one which clearly explains how you’ll use your skills and experience to provide value to the company or public institution looking to hire you. Your resume needs to inspire confidence that you can handle all of the security concerns they might have.
That’s why one technique you might want to use is to research the prospective employer to better understand what specific security concerns they might have. Whether they’re worried about DDoS attacks or private user data getting out, you should aim to address those specific concerns wherever possible. We’ll discuss tailoring your resume in more detail later, but for now, think about how you can make your resume stand out in this way.
What are ideal security analyst job qualifications and how to list them correctly
The base requirements for most security analyst positions will focus on a Bachelor’s degree in a field related to computer science and a few years of IT work experience. Of course, if you’ve been working as a security analyst for many years, you can bypass those basic requirements.
Always pay close attention to the specific requirements for each job and make them prominently visible on your resume. For example, you can mention a degree, required certification, and years of experience in a resume objective or summary (more on how to write those below). The idea is to make it 100% clearer from the beginning that you meet the requirements and should be taken seriously as a candidate.
What to include in your education section
This is where many security analyst resumes go wrong. They waste space listing educational information which just isn’t relevant to their prospective employer. Instead, you should only list relevant education and focus more on certifications and trainings. This is because they are much more likely to be relevant and up-to-date.
BS in Computer Science
The University of Calgary
2004-2009
-3.8 GPA
Most security analysts will include their education simply out of habit, but looking at the example above, what is this really telling a recruiter? This degree is related to digital security work, but it’s old enough that it’s not really worth mentioning if you’ve been working in the field ever since. The GPA is definitely not relevant.
Bachelor of Science in Professional Studies (BSPS) in Information Security
The University of Richmond
2015-2019
This example is more recent and the degree is more closely related to security analyst work, so it’s worth including.
Why certifications are more important for security analysts
As mentioned, certifications are generally more valuable because they are more focused than a formal degree. Looking at the information security degree example above, all you really know is that this person studied general information security. The certifications listed below, however, tell the recruiter that you have very specific skills.
These are the top certifications you should consider obtaining:
- Certified Ethical Hacker
- CWAPT Certified Penetration Tester
- Certified Reverse Engineering Analyst
- CompTIA Network+
How to make your achievements stand out
Far too often, security analyst resumes will focus on listing their responsibilities. The problem is, being responsible for digital security somewhere doesn’t mean you did a good job. Plenty of institutions get away with being lucky that they aren’t targeted by malicious actors. To get a better sense of you as a candidate, it’s best to try and list concrete accomplishments instead.
Responsible for cybersecurity at Forager Systems Inc.
Remember, this company could have been the victim of a terrible cyber attack and this statement would still be true. That’s why framing your achievements and experience this way doesn’t work.
Took over cybersecurity at Forager Systems Inc. and implemented phishing tests, led company-wide training in updated security protocols, and reduced known security vulnerabilities by 86%.
Here, the focus is more on what the candidate did specifically. Showing concrete achievements is hard for a security analyst because your wins are mostly in what you prevent from happening, so focusing on the proactive steps you took is often the best way to go.
How to list your skills
When including your skills you want to follow the same general rules you used for your achievements: using concrete examples. After all, anyone can simply list a bunch of skills (particularly when you’re talking about soft skills) but these lists aren’t going to have much of an impact on recruiters. By giving examples when possible, you’ll force recruiters to really take notice and feel confident that you really possess those skills.
Let’s look at two examples to see what this looks like in practice.
Team player
Because security analysts often have to work on teams or at least coordinate with others within the company or organization, this is a critical skill. But again, listing it doesn’t mean very much. Let’s see what this looks like with an example.
Team player
Organized biannual team building retreats for the digital security team
While it’s hard to “prove” someone is a team player, this example shows them going out of their way to develop a more cohesive team. At the very least, this doesn’t sound like someone who is strongly disliked by their colleagues and thinks team dynamics are important.
The best security analyst hard skills to mention
As mentioned, the most important skills will always vary based on the specific position, but these are the general skills most employers are looking for when hiring a security analyst.
- Ethical hacking
- Cloud computing
- Familiarity with Linux, Unix, and Windows OS
- Security logs
- Network monitoring
- Security Information and Events Management (SIEM)
- Designing security training for employees
- Phishing testing
- TCP/IP
- Firewall protection
- Antivirus and malware systems
The best security analyst soft skills to mention
- Proactive
- Attention to detail
- Works well on a team
- Good written and oral communication
- Works well under pressure
- Creative problem solving/troubleshooting
Why your resume should start with an objective or summary
As mentioned at the beginning, it’s vital to get the most important information across to the recruiter as quickly as possible. But considering most resume sections are dedicated to one specific type of information, you need something more flexible to communicate all of your top qualities.
This is where a resume objective or summary comes in. These sections are flexible enough to allow you to make a strong first impression by focusing the recruiter’s attention on the reasons you’re an ideal candidate for that position. The main difference between them is in length. You generally want to use an objective if you don’t feel the need to explain very much or if your application includes a cover letter.
If you want to explain more about your qualifications right at the start or explain something like the reason for a career change, a longer resume summary is best. Below you’ll find some examples to show you how to write each.
How to write a resume objective
An objective is a single sentence focused on explaining who you are and what you aim to achieve with this specific resume. It should be concise and dense with useful information. The last thing you want is a recruiter needing to re-read your objective to understand it or wondering why you included it in the first place.
As an experienced security analyst I’m ready to ensure your company’s cyber security is up to my high standards and your data is protected.
While this example does focus on the value this candidate will provide, a nice focus, it makes several other critical mistakes. First, it’s written in the first person instead of the third person. But more importantly, it’s vague about the person’s experience while sounding a bit arrogant. This would likely play into the nightmare scenario of hiring a security analyst who’s difficult to work with. Contrast that with this example.
Security analyst with 8 years experience in training employees to improve security protocols and hacker protection looking to improve data protection at Imagine Software.
With this example we get a clear idea about what kind of experience this candidate has and what they hope to achieve with it.
How to write a resume summary
While resume summaries should follow many of the rules resume objectives do, the main thing to point out is that just because they tend to be longer doesn’t mean you should get wordy. Keep your summary focused and on-point.
Security analyst with many years experience working for companies like Intel, Helios Systems, Rise Inc., and Jackpot Solutions. Helped companies large and small respond to crisis situations and improve network security.
Here, the candidate starts by wasting space listing companies they’ve worked for (information which can easily be included elsewhere) alongside vague descriptions of their experience and accomplishments. After reading this, a recruiter won’t feel they have a real sense of this person as a candidate. They will mostly be left with unanswered questions about how they “helped” these companies and what resulted from their work there.
Security analyst with 12 years experience working with industry leaders like Intel develop data breach crisis response plans, leading small teams to proactively test for vulnerabilities, and develop new authentication systems for hundreds of network uses.
Instead of wasting space, this example gets right to the core reasons they should be hired. As a recruiter, you instantly know how much experience they have and what kinds of security work they’ve done. In just a few lines, you get a sense of them as a candidate. That’s what you should be aiming for with your resume summary.
How to target your resume for each application
As alluded to above, it’s important to create a custom resume for each security analyst position you need a resume for. The reason is that this allows you to customize the skills, achievements, and other elements of your resume to fit the needs of that specific employer. It means more work but the higher chances of getting a better job more than make up for it.
Beyond having a better resume, this also communicates that the candidate is willing to take the time to do things the right way (a critical quality for a great security analyst).
How to prepare for a job interview as a security analyst
Because so many of the key skills involved with being a security analyst are hard to demonstrate on a resume (certifications can only do so much) you can expect a job interview to test you on your technical knowledge. The interviewer will also likely try and get a sense of you as a worker, whether you work well on a team and with the non-technical staff who you’ll need to interact with regularly.
The key to being prepared is being comfortable and having the right answers ready. Getting there requires practice. Use the list of likely questions provided below and try to brainstorm some others based on the specifics of this employer. Have a trusted friend or colleague practice with you so you can work on answering them well. This will get you more comfortable with the process as a whole and let you hone your answers until they’re perfect.
Which questions are likely to be asked during the interview process?
- Describe your interest in cyber security.
- Why did you choose to apply here?
- Describe your ideal working environment.
- What do you hope to achieve in this role?
- How would you go about evaluating our greatest security risks?
- If you felt your colleagues here weren’t taking digital security seriously enough, what would you do?
- Can you describe your home network setup?
- Can you explain DNS monitoring to me?
- How would you improve our user authentication practices?
How to make your resume stand out?
If you’ve followed all our advice up to this point, you should already have a standout resume. But there’s one last element you need to really stand out: great design. In a sea of resumes created on Word or Google Docs, some clean and modern design will really stand out (especially because security analysts aren’t known for their design sense).
But if you’re not a designer and your resume should be in one of the three formats mentioned in the beginning, what can you do? In short, use a great resume builder.
Why you should be using a resume builder
From ensuring your resume is ATS ready to giving you easy access to standout design, a resume builder is an essential tool for creating an excellent security analyst resume. It allows you to stop worrying about technical ATS requirements and design so you can focus on improving your resume’s content. But choosing the right resume builder is hard. You don’t want to pick one, spend the time creating a resume, and then find out it doesn’t meet your requirements.
That’s why Resumebuild.com is an easy choice. It’s been built from the ground up just for candidates like you. It’s got an intuitive builder so you can avoid the formatting headaches which can make creating a resume so difficult. When you can focus on what matters with your resume, the result is better resumes and a better job, so what are you waiting for?
security analyst Job Descriptions; Explained
If you're applying for an security analyst position, it's important to tailor your resume to the specific job requirements in order to differentiate yourself from other candidates. Including accurate and relevant information that directly aligns with the job description can greatly increase your chances of securing an interview with potential employers.
When crafting your resume, be sure to use action verbs and a clear, concise format to highlight your relevant skills and experience. Remember, the job description is your first opportunity to make an impression on recruiters, so pay close attention to the details and make sure you're presenting yourself in the best possible light.
security analyst
- Admin of Privileged Identity Management (ARCOS)
- Vulnerabilities & Threat Assessment.
- Involved in Configuration Audit
- Firewall Rule Base review.
- Security Events & Incident Management using PIM Tool.
- Security Systems Implementation.
security analyst
- Encrypt data transmissions and erect firewalls to conceal confidential information as it is being transmitted and to keep out tainted digital transfers.
- Monitor current reports of computer viruses to determine when to update virus protection systems.
- Train users and promote security awareness to ensure system security and to improve server and network efficiency.
- Coordinate implementation of computer system plan with establishment personnel and outside vendors.
- Document computer security and emergency measures policies, procedures, and tests.
security analyst
- Research of malwares’ network traffic
- Develop protections against network traffic of malwares
- Web applications’ analysis
- Data analysis using SQL
- Manage the content of the Anti-Bot product, including urgent releases of zero day protections
- Facilitate the weekly release cycle in coordination with the AB release manager
- Python Programming – Development of integration and automation tools
security analyst
- Performing Dynamic application security testing of the web applications.
- Testing and analysis of bench-marking the application against industry standards such as OWASP Top 10, SANS 25.
- Documenting all the vulnerabilities and providing mitigation and explaining the impact of the vulnerability to the developers and managers.
- Conduct OWASP Top 10 training and Information security awareness programmed to developers and testers.
- Test cases are identified based on security requirements and Company policies.
- Test case coverage include check for Authentication, Authorization, Data Protection, In-formation Leakage, Error handling, Input Validation, Privilege Escalation, Session Management, Audit and Alerts.
- Verifying the user access reconciliation reports, enforcing security quiz compliance, identifying security incidents and its closure, con-ducting spot checks within the accounts, coordinating internal security audits, system security assessments of organizational infrastructure.
senior security analyst
- Onsite at BNP Paribas Bank – (APAC SMC IT Security )
- Real time Identification, Analysis and resolution of security events detected by SIEM tool (ArcSight Ver.6.8.0).
- Understanding with Custom Rules, Reports, Queries, Filters and Dashboards, Active Channels in ArcSight (SIEM tool) as per business requirement.
- Tools use in daily basis : Symantec Data Loss prevention,MATD, WAF,Tripwire, IronPort, ArcSight logger, VirusTotal,
- Different reports analysis i.e. IPS reports, Firewall reports, Unix, Windows, Web server access log analysis etc.
security analyst Job Skills
For an security analyst position, your job skills are a key factor in demonstrating your value to the company and showing recruiters that you're the ight fit for the role. It's important to be specific when highlighting your skills and ensure that they are directly aligned with the job requirements, as this can greatly improve your chances of being hired. By showcasing your relevant skills and experience, you can make a compelling case for why you're the best candidate for the job.
How to include technical skills in your resume:
Technical skills are a set of specialized abilities and knowledge required to perform a particular job
effectively. Some examples of technical skills are data analysis, project management, software proficiency,
and programming languages, to name a few.
Add the technical skills that will get hired in your career
field with our simple-to-use resume builder. Select your desired resume template, once you reach the skills
section of the builder, manually write in the skill or simply click on "Add more skills". This will
automatically generate the best skills for your career field, choose your skill level, and hit "Save &
Next."
- Encryption
- Firewalls
- Cybersecurity
- Vulnerability Analysis
- Network Security
- Incident Response
- Risk Assessment
- Penetration Testing
- Security Monitoring
- Data Loss Prevention
- Endpoint Security
- Security Auditing
- Identity and Access Management
- Intrusion Detection
- Log Analysis
- Malware Analysis
- System Hardening
- Security Architecture
- Identity Management
- Cloud Security
- Hardware Security.
How to include soft skills in your resume:
Soft skills are non-technical skills that relate to how you work and that can be used in any job. Including
soft skills such as time management, creative thinking, teamwork, and conflict resolution demonstrate your
problem-solving abilities and show that you navigate challenges and changes in the workplace
efficiently.
Add competitive soft skills to make your resume stand-out to recruiters! Simply select
your preferred resume template in the skills section, enter the skills manually or use the "Add more skills"
option. Our resume builder will generate the most relevant soft skills for your career path. Choose your
proficiency level for each skill, and then click "Save & Next" to proceed to the next section.
- Communication
- Interpersonal
- Leadership
- Time Management
- Problem Solving
- Decision Making
- Critical Thinking
- Creativity
- Adaptability
- Teamwork
- Organization
- Planning
- Public Speaking
- Negotiation
- Conflict Resolution
- Research
- Analytical
- Attention to Detail
- Self-Motivation
- Stress Management
- Collaboration
- Coaching
- Mentoring
- Listening
- Networking
- Strategic Thinking
- Negotiation
- Emotional Intelligence
- Adaptability
- Flexibility
- Reliability
- Professionalism
- Computer Literacy
- Technical
- Data Analysis
- Project Management
- Customer Service
- Presentation
- Written Communication
- Social Media
- Troubleshooting
- Quality Assurance
- Collaboration
- Supervisory
- Risk Management
- Database Management
- Training
- Innovation
- Documentation
- Accounting
- Financial Management
- Visualization
- Reporting
- Business Acumen
- Process Improvement
- Documentation
- Relationship Management.
How to Improve Your security analyst Resume
Navigating resume pitfalls can mean the difference between landing an interview or not. Missing job descriptions or unexplained work history gaps can cause recruiters to hesitate. Let's not even talk about the impact of bad grammar, and forgetting your contact info could leave your potential employer hanging. Aim to be comprehensive, concise, and accurate.
ernestevans63@protonmail.com
724-762-4428
Employment history
- Design and implement security architectures
- Identify and respond to security incidents
- Monitor security systems and networks for potential threats
- Develop and maintain security awareness training
- Evaluate and recommend security solutions
- Analyze security requirements and recommend appropriate solutions
Education
Skills
Unexplained Year Gaps and Missing Job Experiences are a No-no
Gaps in your resume can prevent recruiters from hiring you if you don't explain them.
Key Insights- It's okay to have gaps in your work experience but always offer a valid explanation instead of just hiding it.
- Use the gap to talk about positive attributes or additional skills you've learned.
- Be honest and straightforward about the gap and explain it using a professional summary.
How to Optimize Your security analyst Resume
Keep an eye out for these resume traps. Neglecting to detail your job roles or explain gaps in your career can lead to unnecessary doubts. Grammar blunders can reflect negatively on you, and without contact information, how can employers reach you? Be meticulous and complete.
Professional Summary
Employment history
- Coorinate an collaberate wit other IT teams.
- Mointor and report on securiyt compliance.
- Perform vulnerabilty an risk assessements.
- Moniter securty sytems nd netwrks fer potental threats.
- Develp security reports and documentaion.
- Evaluatte, and recomend security solutonss.
- Moniter and reporton security complience.
- Prepared and presented security briefings and trainings session.
- Anaylze security riske and develope risk mitigations strategys.
Education
Skills
Avoid Spelling Mistakes and Include your Contact Information
Missing contact information prevents recruiters from understanding you're the best fit for the position.
Key Insights- Make sure you're not missing contact information on your resume. That should include your full name, telephone number and email address.
- Make sure to use a professional email address as part of your contact information.
- Highlight your contact information and double check that everything is accurate to help recruiters get in touch with you.
security analyst Cover Letter Example
A cover letter can be a valuable addition to your job application when applying for an security analyst position. Cover letters provide a concise summary of your qualifications, skills, and experience, also it also gives you an opportunity to explain why you're the best fit for the job. Crafting a cover letter that showcases your relevant experience and enthusiasm for the Accounts Payable role can significantly improve your chances of securing an interview.
Davis davis.mike@protonmail.com
832-665-3599
137 Pleasant St., Herndon, KS
67739
Capgemini
San Jose, California
Greetings Capgemini Recruitment Team
I am a highly motivated Security Analyst with 4 years of experience in Business Strategy & Analysis. I am excited to submit my application for the Senior Security Analyst position at Capgemini, where I believe my skills and expertise would be an excellent fit.
My life experiences have taught me the importance of hard work, dedication, and collaboration. Whether it was on the work, or just personally, I have always been committed to pursuing my goals with passion and tenacity. I am confident that throughout all of these years I have gained the skills and expertise necessary to succeed in this role and be a great asset for Capgemini. I am eager to join a team that shares my values and work towards a common goal.
I am elated about the opportunity to join a team that shares my passion for this field, and values collaboration and innovation. I am confident that together we can overcome whatever tests and challenges are put on our way.
Kindest regards,
Mike Davis
832-665-3599
davis.mike@protonmail.com
Mike Davis
Showcase your most significant accomplishments and qualifications with this cover
letter.
Personalize this cover letter in just few minutes with our user-friendly tool!
Related Resumes & Cover Letters

Build your Resume in 15 minutes
Create an awesome resume that meets the expectations of potential employers with our selection of professional, field-tested resume templates.