Use This Template
Use This Template
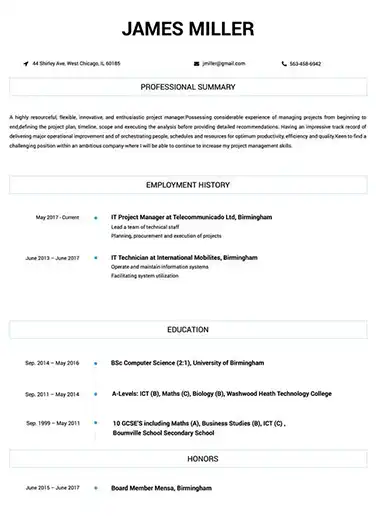
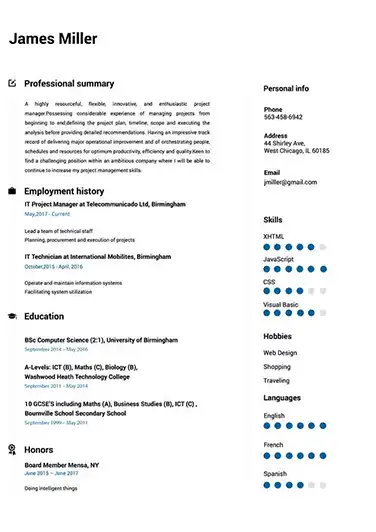
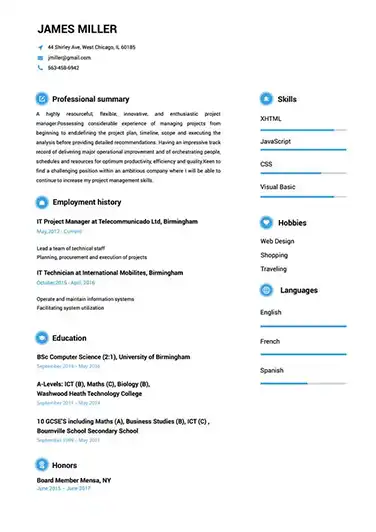
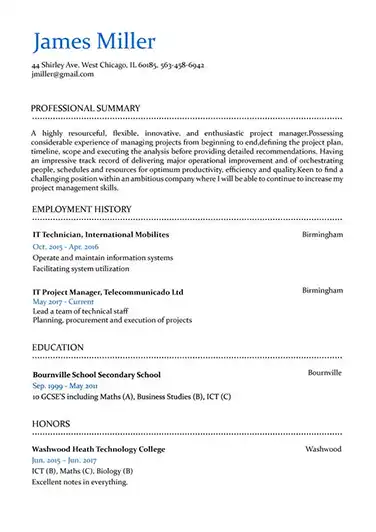
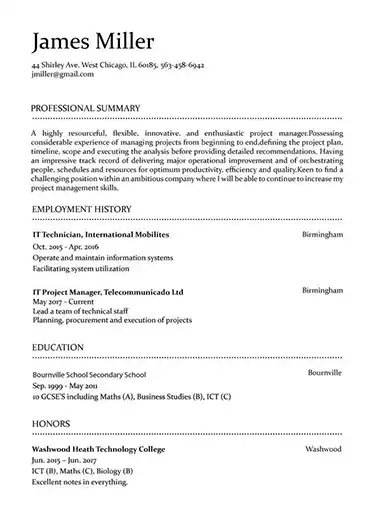
Build your resume in 15 minutes
Create an awesome resume that meets the expectations of potential employers with our selection of professional, field-tested resume templates.
security architect: Resume Samples & Writing Guide
fredevans51@yandex.com
607-585-8754
Employment history
- Maintain records of security incidents and investigations
- Research and recommend new security technologies and solutions
- Provide technical guidance and training on security best practices
- Develop security strategies for cloud and on-premise environments
- Identify and assess security risks and vulnerabilities
- Design, implement, and maintain security architectures, systems, and solutions
- Identify and assess security risks and vulnerabilities
- Analyze security requirements and recommend solutions to mitigate risks
- Implement security measures in accordance with compliance requirements
Education
Skills
Do you already have a resume? Use our PDF converter and edit your resume.
grant_umberto@mail.com
969-546-2463
Employment history
- Collaborate with IT teams to ensure secure system design and operations
- Research and recommend new security technologies and solutions
- Maintain records of security incidents and investigations
Education
Skills
jake_smith@mail.com
755-978-5982
Professional Summary
Employment history
- Lead security audits and assessments
- Collaborate with IT teams to ensure secure system design and operations
- Evaluate and recommend security products and services
- Lead security audits and assessments
- Provide technical guidance and training on security best practices
- Evaluate and recommend security products and services
- Lead security audits and assessments
- Maintain records of security incidents and investigations
- Analyze security requirements and recommend solutions to mitigate risks
Education
Skills
gusyoung74@aol.com
776-591-2103
Professional Summary
Employment history
- Design, implement, and maintain security architectures, systems, and solutions
- Lead security audits and assessments
- Collaborate with IT teams to ensure secure system design and operations
- Identify and assess security risks and vulnerabilities
- Stay abreast of emerging security threats and technologies
- Provide technical guidance and training on security best practices
- Research and recommend new security technologies and solutions
- Identify and assess security risks and vulnerabilities
- Collaborate with IT teams to ensure secure system design and operations
Education
Skills
adamsfrancis@mail.com
857-306-3857
Employment history
- Monitor security systems and networks for intrusions or unauthorized access
- Stay abreast of emerging security threats and technologies
- Develop security policies, standards, and procedures
- Identify and assess security risks and vulnerabilities
- Stay abreast of emerging security threats and technologies
- Implement security measures in accordance with compliance requirements
- Evaluate and recommend security products and services
- Develop and maintain security documentation
- Develop security strategies for cloud and on-premise environments
Education
Skills
Not in love with this template? Browse our full library of resume templates
security architect Job Descriptions; Explained
If you're applying for an security architect position, it's important to tailor your resume to the specific job requirements in order to differentiate yourself from other candidates. Including accurate and relevant information that directly aligns with the job description can greatly increase your chances of securing an interview with potential employers.
When crafting your resume, be sure to use action verbs and a clear, concise format to highlight your relevant skills and experience. Remember, the job description is your first opportunity to make an impression on recruiters, so pay close attention to the details and make sure you're presenting yourself in the best possible light.
security architect
- Enhances security team accomplishments and competence by planning delivery of solutions; answering technical and procedural questions for less experienced team members; teaching improved processes; mentoring team members.
- Determines security requirements by evaluating business strategies and requirements; researching information security standards; conducting system security and vulnerability analyses and risk assessments; studying architecture/platform; identifying integration issues; preparing cost estimates.
- Plans security systems by evaluating network and security technologies; developing requirements for local area networks (LANs), wide area networks (WANs), virtual private networks (VPNs), routers, firewalls, and related security and network devices; designs public key infrastructures (PKIs), including use of certification authorities (CAs) and digital signatures as well as hardware and software; adhering to industry standards.
- Implements security systems by specifying intrusion detection methodologies and equipment; directing equipment and software installation and calibration; preparing preventive and reactive measures; creating, transmitting, and maintaining keys; providing technical support; completing documentation.
- Verifies security systems by developing and implementing test scripts.
- Maintains security by monitoring and ensuring compliance to standards, policies, and procedures; conducting incident response analyses; developing and conducting training programs.
- Upgrades security systems by monitoring security environment; identifying security gaps; evaluating and implementing enhancements.
security architect
- Analyse and understand the requirement specifications provided by the clients.
- Designing the F5 Web Application Firewalls solution.
- Supervising the technical teams during implementation and operations.
- Responsible for overseeing the quality procedures related to the project.
- Project governance
security architect, websphere commerce
- Subject Matter Expert for Security and Member components
- PCI Compliance
- GDPR Compliance
- ISO 27K Compliance
- Primary responder for Product Security Incident Responder Team
- Java development
- LDAP integration
security architect
- Open ID Connect and SAML integration
security architect Job Skills
For an security architect position, your job skills are a key factor in demonstrating your value to the company and showing recruiters that you're the ight fit for the role. It's important to be specific when highlighting your skills and ensure that they are directly aligned with the job requirements, as this can greatly improve your chances of being hired. By showcasing your relevant skills and experience, you can make a compelling case for why you're the best candidate for the job.
How to include technical skills in your resume:
Technical skills are a set of specialized abilities and knowledge required to perform a particular job
effectively. Some examples of technical skills are data analysis, project management, software proficiency,
and programming languages, to name a few.
Add the technical skills that will get hired in your career
field with our simple-to-use resume builder. Select your desired resume template, once you reach the skills
section of the builder, manually write in the skill or simply click on "Add more skills". This will
automatically generate the best skills for your career field, choose your skill level, and hit "Save &
Next."
- Encryption
- Firewalls
- Cloud Security
- Cybersecurity
- Security Protocols
- Intrusion Detection
- Security Auditing
- Vulnerability Scanning
- Security Architecture
- Identity and Access Management
- Security Best Practices
- Network Security
- Security Compliance
- Penetration Testing
- Risk Analysis
- Security Operations
- Systems Analysis
- Incident Response
- Security Monitoring
- Security Tools.
How to include soft skills in your resume:
Soft skills are non-technical skills that relate to how you work and that can be used in any job. Including
soft skills such as time management, creative thinking, teamwork, and conflict resolution demonstrate your
problem-solving abilities and show that you navigate challenges and changes in the workplace
efficiently.
Add competitive soft skills to make your resume stand-out to recruiters! Simply select
your preferred resume template in the skills section, enter the skills manually or use the "Add more skills"
option. Our resume builder will generate the most relevant soft skills for your career path. Choose your
proficiency level for each skill, and then click "Save & Next" to proceed to the next section.
- Communication
- Interpersonal
- Leadership
- Time Management
- Problem Solving
- Decision Making
- Critical Thinking
- Creativity
- Adaptability
- Teamwork
- Organization
- Planning
- Public Speaking
- Negotiation
- Conflict Resolution
- Research
- Analytical
- Attention to Detail
- Self-Motivation
- Stress Management
- Collaboration
- Coaching
- Mentoring
- Listening
- Networking
- Strategic Thinking
- Negotiation
- Emotional Intelligence
- Adaptability
- Flexibility
- Reliability
- Professionalism
- Computer Literacy
- Technical
- Data Analysis
- Project Management
- Customer Service
- Presentation
- Written Communication
- Social Media
- Troubleshooting
- Quality Assurance
- Collaboration
- Supervisory
- Risk Management
- Database Management
- Training
- Innovation
- Documentation
- Accounting
- Financial Management
- Visualization
- Reporting
- Business Acumen
- Process Improvement
- Documentation
- Relationship Management.
How to Improve Your security architect Resume
Navigating resume pitfalls can mean the difference between landing an interview or not. Missing job descriptions or unexplained work history gaps can cause recruiters to hesitate. Let's not even talk about the impact of bad grammar, and forgetting your contact info could leave your potential employer hanging. Aim to be comprehensive, concise, and accurate.
adamjohnson@outlook.com
869-518-0593
Employment history
- Lead security audits and assessments
- Identify and assess security risks and vulnerabilities
- Develop security strategies for cloud and on-premise environments
- Design, implement, and maintain security architectures, systems, and solutions
- Develop security policies, standards, and procedures
- Lead security audits and assessments
Education
Skills
Unexplained Year Gaps and Missing Job Experiences are a No-no
Gaps in your resume can prevent recruiters from hiring you if you don't explain them.
Key Insights- It's okay to have gaps in your work experience but always offer a valid explanation instead of just hiding it.
- Use the gap to talk about positive attributes or additional skills you've learned.
- Be honest and straightforward about the gap and explain it using a professional summary.
How to Optimize Your security architect Resume
Keep an eye out for these resume traps. Neglecting to detail your job roles or explain gaps in your career can lead to unnecessary doubts. Grammar blunders can reflect negatively on you, and without contact information, how can employers reach you? Be meticulous and complete.
Employment history
- Reasearch and recomend new securitie technolgies and solutuions
- Analyze securitie requirments and recomend solutuons to mitgate riskss
- Develop securitie stragies for cloud and on-premise enviromentss
- Maintain records of security incidents and investigations
- Design, implement, and maintain security architectures, system, and solutionss
- Collaborate with IT teams to ensure secure system design and operation's
- Implement security measurs in accrodance with compilance requirments
- Provied technicl guidane and trainning on security best practices
- Develope security strategys for cloud and on-premise enviroments
Education
Skills
Avoid Spelling Mistakes and Include your Contact Information
Missing contact information prevents recruiters from understanding you're the best fit for the position.
Key Insights- Make sure you're not missing contact information on your resume. That should include your full name, telephone number and email address.
- Make sure to use a professional email address as part of your contact information.
- Highlight your contact information and double check that everything is accurate to help recruiters get in touch with you.
security architect Cover Letter Example
A cover letter can be a valuable addition to your job application when applying for an security architect position. Cover letters provide a concise summary of your qualifications, skills, and experience, also it also gives you an opportunity to explain why you're the best fit for the job. Crafting a cover letter that showcases your relevant experience and enthusiasm for the Accounts Payable role can significantly improve your chances of securing an interview.
Evans fredevans51@yandex.com
607-585-8754
270 Millwood Drive, Blumengard Colony, SD
57438
Oracle
Redwood City, California
To the Recruitment Team at Oracle
I am a highly motivated and experienced Security Architect with 9 years of experience in Information Technology (IT). I am excited to apply for the Senior Security Architect position at Oracle, where I am confident that I can contribute to your organization's success.
My diverse life experiences have taught me the importance of adaptability, creativity, and resilience. Whether it was on the job, or simply on my day to day, I have learned to navigate challenges and find innovative solutions. I am confident that I possess the skills and expertise necessary to excel in the position at Oracle and I am excited about the opportunity to grow with a team that values these qualities and contribute to your organization's growth and success.
I appreciate the time and consideration you have given my application. I am confident that if we work together we could achieve great things and so I look forward to the opportunity to join your team.
Kind regards,
Fred Evans
607-585-8754
fredevans51@yandex.com
Fred Evans
Showcase your most significant accomplishments and qualifications with this cover
letter.
Personalize this cover letter in just few minutes with our user-friendly tool!
Related Resumes & Cover Letters

Build your Resume in 15 minutes
Create an awesome resume that meets the expectations of potential employers with our selection of professional, field-tested resume templates.